Mitigating Risk at Every Stage of the Product Development Lifecycle

Table of Contents
- Introduction
- Understanding the Product Development Lifecycle
- Why Risk Management Matters Throughout Development
- Risk Mitigation in Discovery and Ideation
- Risk Management During Design and Planning
- Development Phase Risk Controls
- Testing and Quality Assurance Risks
- Launch and Deployment Risk Mitigation
- Post-Launch Monitoring and Maintenance
- Risk Management for SaaS Product Development Lifecycle
- Conclusion
Your team invested months building a product users don’t want. Features took twice as long to develop as planned. Security vulnerabilities discovered after launch cost millions to fix. Technical debt accumulated so quickly that velocity ground to a halt within six months.
Product development failures manifest in countless ways:
- Launching products that miss market needs entirely.
- Exceeding budgets significantly due to poor planning.
- Discovering critical flaws only after customer adoption.
- Building technical foundations that cannot scale.
- Missing competitive windows while competitors ship faster.
The solution lies in systematic risk mitigation throughout the product development lifecycle. Rather than treating risk management as a final checklist item, successful teams embed protective practices into every phase, from concept through maintenance.
Keep reading as we examine how to identify and mitigate risks at each stage of product development, preventing costly failures before they occur.
Understanding the Product Development Lifecycle
The product development lifecycle encompasses all stages from initial concept through ongoing maintenance and iteration. This framework provides structure for transforming ideas into market-ready products while managing complexity and uncertainty.
Most product development follows these fundamental stages of the product development life cycle:
Discovery and Research
This initial phase focuses on identifying viable market opportunities, understanding user needs through research and interviews, and validating concepts worth pursuing before significant investment. Teams conduct market analysis, competitive research, and customer discovery to ensure proposed products solve real problems for defined audiences. This phase prevents the costly mistake of building products nobody wants.
Planning and Design
Once concepts are validated, this phase defines detailed requirements, creates technical specifications, and designs solutions that address validated problems. Teams produce wireframes, prototypes, architecture diagrams, and project plans. Planning establishes the roadmap for execution, while design creates blueprints guiding development teams. Thorough planning prevents misunderstandings and rework later.
Development and Implementation
During this phase, teams build the product according to specifications with iterative refinement based on testing and feedback. Engineers write code, integrate components, and create working software. Development transforms designs into functional products through systematic construction following established practices and standards.
Testing and Quality Assurance
This critical phase validates that products work correctly, meet requirements, and deliver acceptable user experiences. Teams conduct various testing types, including functional, performance, security, and usability testing. Quality assurance catches defects before users encounter them, preventing reputation damage and costly post-launch fixes.
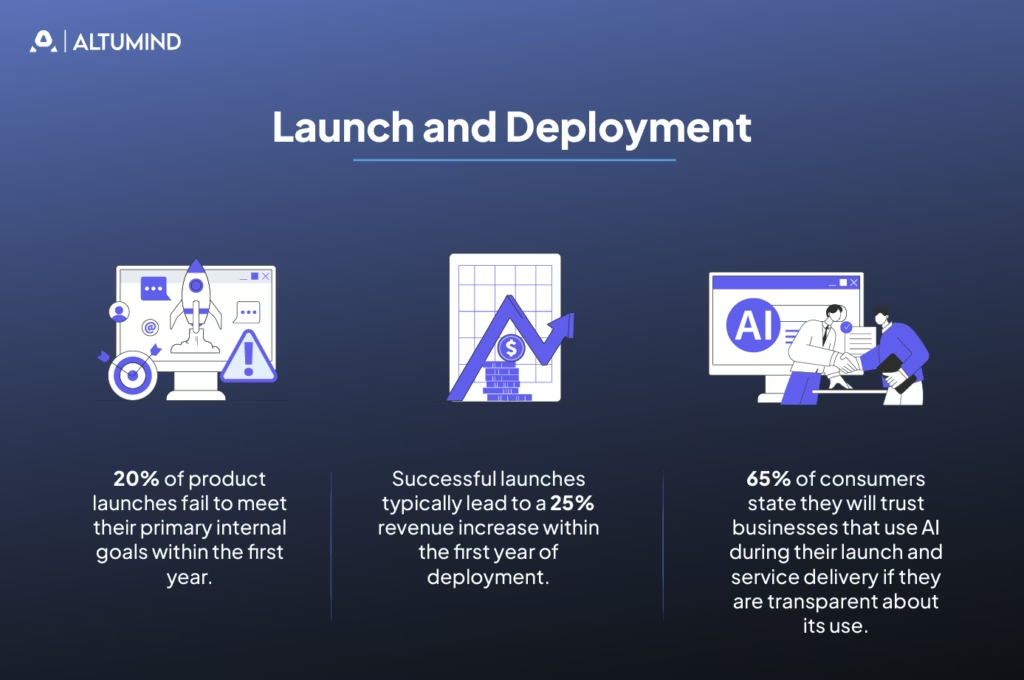
Launch and Deployment
This phase releases products to users with appropriate marketing, support infrastructure, and monitoring systems. Teams execute deployment plans, activate support channels, and begin tracking product performance. Launch transition products from controlled development environments to real-world usage.
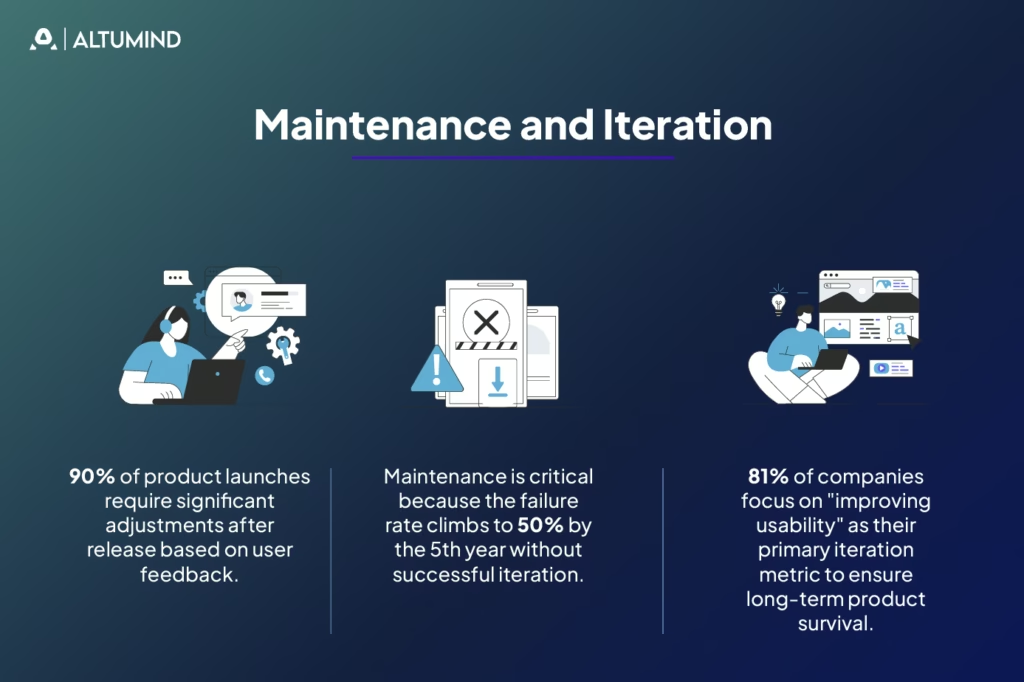
Maintenance and Iteration
Post-launch activities support deployed products while continuously improving based on usage data, user feedback, and evolving requirements. Teams fix bugs, release updates, add features, and optimize performance. Maintenance ensures products remain valuable and competitive over time.
Why Risk Management Matters Throughout Development
Each phase of the product development life cycle introduces unique risks that compound if left unaddressed. Discovery phase risks lead to building the wrong product. Design risks create flawed foundations. Development risks accumulate technical debt. Testing gaps allow defects to reach users. Launch risks damage reputation and revenue.
Early risk identification and mitigation cost far less than addressing problems after they materialize. A requirement error caught in planning might take hours to fix. The same error discovered after launch could require weeks of rework, affecting thousands of users.
Systematic risk management transforms product development from reactive firefighting into proactive problem prevention. Teams anticipate challenges, plan mitigations, and build resilience into products from inception.
Risk Mitigation in Discovery and Ideation
The discovery phase determines whether you build the right product. Risks here center on market understanding, customer needs, and strategic alignment.
ValidateMarket Demand Early
Many products fail because they solve problems nobody has or address markets too small to sustain businesses. Rigorous market validation prevents wasting resources on doomed concepts.
Validation activities include:
- Customer Interviews: Speaking directly with potential users to understand their problems, workflows, and needs.
- Competitive Analysis: Evaluating existing solutions to identify gaps, weaknesses, and opportunities for differentiation.
- Market Sizing: Quantifying addressable markets to ensure opportunities justify investment.
- Willingness to Pay: Testing whether customers will actually pay prices supporting viable business models.
Strong product discovery practices reduce the risk of building products that never find product-market fit.
IdentifyTechnical Feasibility Constraints
Not every concept can be built with available technology, budget, or timeline. A technical feasibility assessment identifies constraints before committing to impossible goals.
Feasibility evaluation examines the following:
- Technology Availability: Whether required technologies exist and are accessible.
- Performance Requirements: If solutions can meet speed, scale, and reliability needs.
- Integration Complexity: How difficult connecting to existing systems will be.
- Skill Availability: Whether teams have or can acquire necessary expertise.
Early technical consultation prevents pursuing architecturally impossible concepts or discovering fundamental limitations after significant investment.
Assess Resource Requirements Realistically
Underestimating required time, budget, or people creates cascading problems throughout development. Realistic resource assessment based on comparable projects prevents chronic under-resourcing.
Resource planning considers:
- Development Effort: Coding, testing, and deployment work required.
- Design Resources: User research, interface design, and prototyping needs.
- Infrastructure Costs: Hosting, services, and tool expenses.
- Ongoing Maintenance: Support and enhancement burden after launch.
Buffer estimates account for unknowns and inevitable surprises. Projects rarely go exactly as planned.
Define Clear Success Metrics
Products without defined success metrics lack direction and accountability. Clear metrics established during discovery guide decisions throughout development and enable objective evaluation after launch.
Success metrics should include:
- Business Outcomes: Revenue, cost savings, or efficiency improvements are expected.
- User Adoption: Number of users who will use the product and how often.
- Performance Targets: Speed, reliability, and quality standards.
- Time to Value: How quickly users and businesses realize benefits.
Metrics provide objective criteria for go/no-go decisions at each development gate.

Risk Management During Design and Planning
The design and planning phase translates validated concepts into detailed specifications and architectural plans. Risks here involve incomplete requirements, flawed architecture, and unrealistic schedules.
Create Comprehensive Requirements Documentation
Incomplete or ambiguous requirements cause misunderstandings, rework, and scope creep. Thorough documentation ensures shared understanding across teams.
Effective requirements specify:
- Functional Capabilities: What the product must do in specific, testable terms.
- Non-Functional Requirements: Performance, security, scalability, and usability standards.
- User Stories: Concrete scenarios describing how users accomplish goals.
- Acceptance Criteria: Objective conditions for considering features complete.
Requirements should be specific enough to guide implementation while flexible enough to accommodate learnings during development.
Design Scalable Technical Architecture
Architecture decisions made early constrain possibilities throughout a product’s lifetime. Poor architectural foundations create technical debt that eventually limits growth and requires expensive rebuilding.
Architecture planning addresses:
- Scalability: How the system handles growth in users, data, and transactions.
- Maintainability: How easily teams can modify and enhance the system over time.
- Security: How the architecture protects data and prevents unauthorized access.
- Integration: How the system connects with external services and data sources.
Involve experienced architects early to establish sound foundations. Digital product development requires technical excellence from inception to avoid costly refactoring later.
Build Realistic Project Schedules
Overly optimistic schedules create pressure leading to shortcuts, technical debt, and quality problems. Realistic schedules based on team capacity and historical velocity prevent chronic delays.
Schedule development considers:
- Historical Velocity: How quickly teams have delivered similar work previously.
- Dependency Management: External dependencies and coordination requirements.
- Buffer for Unknowns: Time reserves for inevitable surprises and learning.
- Stakeholder Availability: Review cycles and approval processes.
Include explicit time for quality activities like code review, testing, and documentation rather than treating them as optional.
Conduct Design Reviews and Validation
Design reviews catch problems before development begins when changes cost the least. Multiple perspectives identify issues individual designers miss.
Review processes include:
- Technical Reviews: Architects evaluate feasibility, scalability, and maintainability.
- Usability Reviews: UX specialists assess interface designs for user-friendliness.
- Security Reviews: Security experts identify vulnerabilities in proposed designs.
- Business Reviews: Stakeholders confirm designs align with business requirements.
Iterate designs based on feedback before committing development resources.

Development Phase Risk Controls
The development phase transforms designs into working software. Risks here involve code quality, technical debt, integration challenges, and scope management.
Implement Rigorous Code Review Practices
Code review catches defects, knowledge gaps, and technical debt before they reach production. Multiple reviewers examining code improve quality and share knowledge across teams.
Effective code review includes:
- Automated Checks: Linters and static analysis tools catch common problems automatically.
- Peer Review: Colleagues review logic, style, and potential issues.
- Security Review: Security-focused reviews identify vulnerabilities.
- Documentation Review: Ensuring code includes adequate comments and documentation.
Treat code review as essential rather than optional. Quality problems caught in review cost far less than those found after deployment.
Manage Technical Debt Deliberately
Technical debt accumulates when teams take shortcuts for speed. Some debt is acceptable and strategic, but unmanaged debt eventually makes systems unmaintainable.
Technical debt management includes:
- Debt Tracking: Documenting shortcuts taken and why.
- Debt Budget: Allocating time each sprint for debt reduction.
- Debt Assessment: Evaluating impact and prioritizing repayment.
- Prevention: Avoiding unnecessary debt through adequate time allocation.
Balance delivery speed against long-term maintainability. Excessive debt eventually slows delivery more than time invested in quality.
Implement Continuous Integration and Testing
Continuous integration catches integration problems immediately rather than allowing them to accumulate. Automated testing provides confidence that changes don’t break existing functionality.
CI/CD practices include:
- Automated Build: Every code commit triggers automatic builds and basic tests.
- Automated Testing: Unit, integration, and regression tests run automatically.
- Deployment Automation: Consistent, repeatable deployment processes.
- Fast Feedback: Developers learn about problems within minutes.
Early problem detection enables quick fixes before issues compound or affect other team members.
Control Scope and Manage Changes
Scope creep occurs when requirements expand continuously during development. Uncontrolled changes delay delivery, increase costs, and introduce new risks.
Scope management includes:
- Change Control Process: Formal evaluation of proposed requirement changes.
- Impact Assessment: Understanding cost and schedule implications before approving changes.
- Priority Management: Deferring lower-priority items rather than expanding scope.
- Stakeholder Communication: Clear explanation of trade-offs when requirements change.
Every added feature delays delivery and introduces new defect opportunities. Question whether changes provide sufficient value to justify delay.
Testing and Quality Assurance Risks
Testing validates that products work correctly and meet requirements. Inadequate testing allows defects to reach users, damaging reputation and requiring expensive fixes.
Implement Comprehensive Test Coverage
Test coverage ensures that testing validates all critical functionality and common user scenarios. Gaps in coverage allow defects to hide until users discover them.
Testing layers include the following:
- Unit Tests: Validating individual components work correctly in isolation.
- Integration Tests: Verifying components work together properly.
- System Tests: Confirming complete systems meet functional requirements.
- User Acceptance Tests: Validating that products meet business needs.
Prioritize testing for critical paths, high-risk areas, and frequently used features over achieving arbitrary coverage percentages.
Conduct Performance and Load Testing
Products that work fine with small data sets and light loads often fail under production conditions. Performance testing identifies scalability problems before users experience them.
Performance validation includes:
- Load Testing: Verifying systems handle expected user volumes.
- Stress Testing: Determining breaking points and degradation patterns.
- Endurance Testing: Confirming stability over extended operation.
- Spike Testing: Validating handling of sudden load increases.
Test under realistic conditions with production-like data volumes and user patterns.
Perform Security Testing and Vulnerability Assessment
Security vulnerabilities create legal liability, damage reputation, and expose customer data. Security testing identifies weaknesses before attackers exploit them.
Security validation includes:
- Vulnerability Scanning: Automated tools identifying known security issues.
- Penetration Testing: Simulated attacks finding exploitable weaknesses.
- Code Security Review: Manual review of security-critical code.
- Third-Party Audit: Independent security assessment providing objective validation.
Address security issues before launch. Post-launch security incidents cost far more than pre-launch fixes.
Include Usability Testing with Real Users
Products passing functional tests can still fail due to poor usability. Real user testing identifies confusion, inefficiency, and frustration that internal testing misses.
Usability testing includes:
- Task-Based Testing: Watching users attempt realistic tasks.
- Think-Aloud Protocol: Users verbalize thoughts while interacting.
- Metrics Collection: Measuring task completion rates and times.
- Feedback Gathering: Understanding what users find confusing or frustrating.
Test with representative users, not just internal team members who know the product intimately.
Launch and Deployment Risk Mitigation
Launch transition products from controlled development environments to production serving real users. Risks involve deployment failures, performance issues, and inadequate support readiness.
Implement Staged Rollout Strategies
Releasing to all users simultaneously magnifies the impact of undiscovered problems. Staged rollouts limit exposure while validating production readiness.
Rollout strategies include:
- Internal Release: Deploy to company employees first.
- Beta Release: Limited release to willing early adopters.
- Phased Release: Gradually expand the user base over days or weeks.
- Geographic Rollout: Release to regions sequentially.
- Feature Flags: Control feature visibility independently from deployment.
Staged approaches enable learning and adjustment before full exposure.
Prepare Comprehensive Monitoring
You cannot fix problems you don’t know about. Comprehensive monitoring detects issues immediately so teams can respond before significant user impact.
Monitoring includes:
- Application Performance: Response times, error rates, and throughput.
- Infrastructure Health: Server resources, network, and database performance.
- User Behavior: Usage patterns, feature adoption, and workflows.
- Business Metrics: Conversions, revenue, and key performance indicators.
Establish baselines before launch to recognize abnormal patterns quickly. Leveraging predictive data and analytics helps identify potential issues before they impact users significantly.
Ensure Support Team Readiness
Support teams encounter problems first when users struggle. Unprepared support creates poor first impressions and extends problem resolution.
Support preparation includes the following:
- Product Training: Support teams understanding product functionality thoroughly.
- Documentation: Comprehensive guides for common tasks and troubleshooting.
- Escalation Processes: Clear paths for routing issues requiring engineering involvement.
- Knowledge Base: Self-service resources reducing support burden.
Brief support teams extensively before launch rather than expecting them to learn while handling frustrated users.
Create Rollback Plans
Not every launch goes smoothly. Rollback plans enable quick return to previous stable versions when problems prove more severe than anticipated.
Rollback planning includes:
- Version Management: Maintaining the ability to deploy previous versions.
- Data Migration: Plans for handling data created in new versions.
- Communication Plans: Messaging to users about rollbacks and fixes.
- Decision Criteria: Clear conditions triggering rollback decisions.
Test rollback procedures before launch to ensure they work when needed.
Post-Launch Monitoring and Maintenance
Launch is not the end of product development but the beginning of ongoing enhancement and maintenance. Post-launch risks involve technical failures, security vulnerabilities, and evolving user needs.
Establish Incident Response Processes
Incidents will occur despite prevention efforts. Effective response processes minimize impact and enable rapid recovery.
Incident management includes:
- Detection and Alerting: Quickly identifying when problems occur.
- Triage and Prioritization: Determining severity and appropriate response urgency.
- Communication: Keeping stakeholders informed during incidents.
- Root Cause Analysis: Understanding why incidents occurred to prevent recurrence.
Practice incident response through drills before real incidents create pressure.
Maintain Security Patching and Updates
New vulnerabilities emerge continuously in dependencies and platforms. Regular patching prevents exploitation of known weaknesses.
Patch management includes:
- Vulnerability Monitoring: Tracking security advisories for used components.
- Patch Testing: Validating updates don’t break functionality.
- Deployment Schedules: Regular maintenance windows for updates.
- Emergency Procedures: Fast paths for critical security fixes.
Automate patching where possible to reduce manual burden and ensure consistency.
Collect and Act on User Feedback
User feedback reveals problems and opportunities invisible to internal teams. Systematic feedback collection and analysis drives continuous improvement.
Feedback mechanisms include the following:
- In-App Feedback: Easy ways for users to report issues or suggestions.
- Usage Analytics: Quantitative data about feature adoption and workflows.
- Support Ticket Analysis: Patterns in user problems and questions.
- Customer Interviews: Deep understanding of user experiences and needs.
Close feedback loops by acting on insights and communicating improvements to users.
Plan for Scalability and Growth
Successful products attract more users and data over time. Systems designed for initial launch often struggle under growth.
Scalability planning includes:
- Capacity Monitoring: Tracking resource utilization trends.
- Performance Optimization: Continuous improvement of efficiency.
- Architecture Evolution: Refactoring as scaling reveals limitations.
- Cost Management: Ensuring infrastructure costs scale appropriately with value.
Address scalability before reaching limits rather than scrambling during growth crises.
Risk Management for SaaS Product Development Lifecycle
The SaaS product development lifecycle introduces unique risks around multi-tenancy, continuous delivery, subscription business models, and customer data protection.
Implement Multi-Tenant Security Isolation
SaaS products serve multiple customers from shared infrastructure. Data isolation failures could expose one customer’s data to others, creating catastrophic security and compliance problems.
Multi-tenant security includes:
- Data Segregation: Ensuring customers cannot access others’ data.
- Resource Isolation: Preventing one customer from exhausting shared resources.
- Access Control: Verifying permissions at every data access.
- Audit Logging: Tracking all data access for security review.
Test isolation thoroughly with penetration testing specifically targeting multi-tenant boundaries.
Enable Continuous Delivery Without Disruption
SaaS products require frequent updates without disrupting service. Deployment strategies must enable change while maintaining availability.
Continuous delivery for SaaS includes:
- Blue-Green Deployments: Switching traffic between environments.
- Canary Releases: Gradually shifting users to new versions.
- Feature Flags: Controlling feature availability independently from code deployment.
- Database Migrations: Updating schemas without downtime.
Test deployment procedures regularly to ensure they work under pressure.
Manage Subscription Business Model Risks
SaaS subscription models create unique business risks. Customer churn directly impacts revenue. Pricing mistakes can doom profitability.
Business model risk management includes:
- Churn Analysis: Understanding why customers cancel and addressing root causes.
- Pricing Validation: Testing price sensitivity and value perception.
- Customer Success: Proactive engagement ensuring customers achieve value.
- Expansion Revenue: Identifying opportunities to grow account value over time.
Monitor customer health metrics and intervene before churn rather than reacting after cancellation.
Ensure Compliance and Data Protection
SaaS products handling customer data face complex compliance requirements varying by industry and region. Violations create legal liability and damage trust.
Compliance management includes:
- Regulatory Assessment: Identifying applicable regulations and standards.
- Privacy by Design: Building data protection into architecture.
- Compliance Monitoring: Regular audits verifying continued compliance.
- Incident Response: Procedures for handling data breaches.
Consult legal and compliance experts early rather than discovering requirements after launch.
Conclusion
Successful product development requires managing risk at every stage, not treating it as a final checklist item. Each phase brings specific risks. If ignored, these risks compound. If addressed early, they remain controlled and predictable.
A structured approach across the product development lifecycle leads to products that meet user needs, perform reliably, and deliver measurable business value. Teams that embed risk mitigation into standard workflows reduce rework, shorten delivery cycles, and improve market outcomes.
Risk management is not overhead. It prevents costly failures, protects timelines, and improves product quality. This discipline is especially critical in SaaS product development, where multi-tenant architecture, continuous delivery, and subscription models increase technical and operational complexity.
Altumind helps organizations implement comprehensive risk management practices across the product development lifecycle. Our digital product development services combine technical excellence with systematic risk mitigation to guarantee products launch successfully and scale sustainably. Build risk-resilient products from day one. Partner with us to turn product uncertainty into predictable success!
Table of Contents
- Introduction
- Understanding the Product Development Lifecycle
- Why Risk Management Matters Throughout Development
- Risk Mitigation in Discovery and Ideation
- Risk Management During Design and Planning
- Development Phase Risk Controls
- Testing and Quality Assurance Risks
- Launch and Deployment Risk Mitigation
- Post-Launch Monitoring and Maintenance
- Risk Management for SaaS Product Development Lifecycle
- Conclusion
Let's Connect
Reach out and explore how we can co-create your digital future!